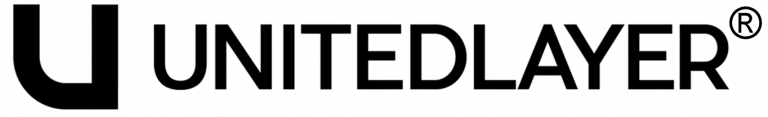
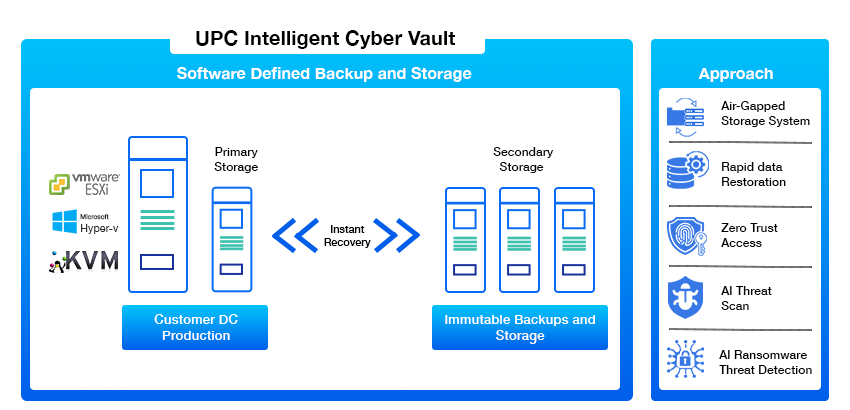
Network Isolation
Zero-trust segmentation ensuring complete production and vault separation
Segmented Vault Network
No Direct Trust Relationship
Restricted Management Plane Access
Zero-Trust Administrative Controls
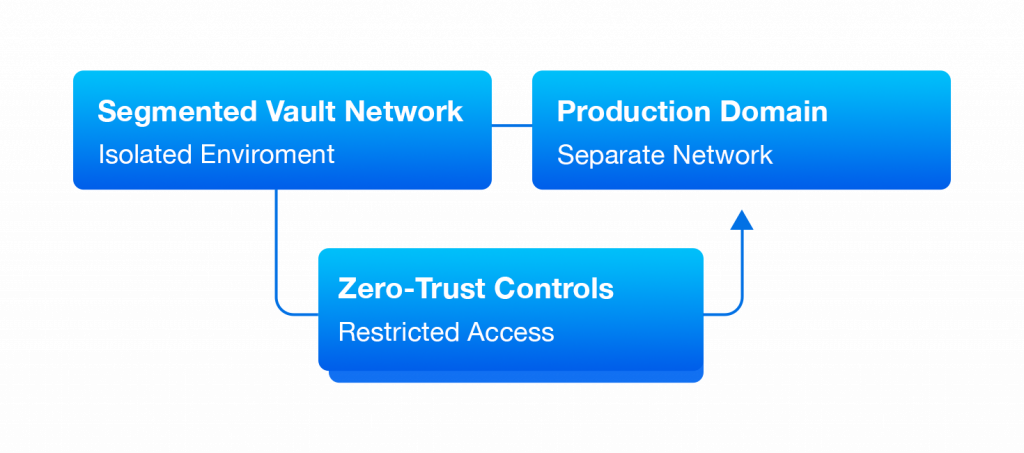
Immutable Storage
Policy-locked immutable storage with end-to-end encryption enforcement
WORM-enabled object storage
Time-bound immutability policies
AES-256 encryption at rest
TLS-secured backup ingestion
Ransomware-Resilient
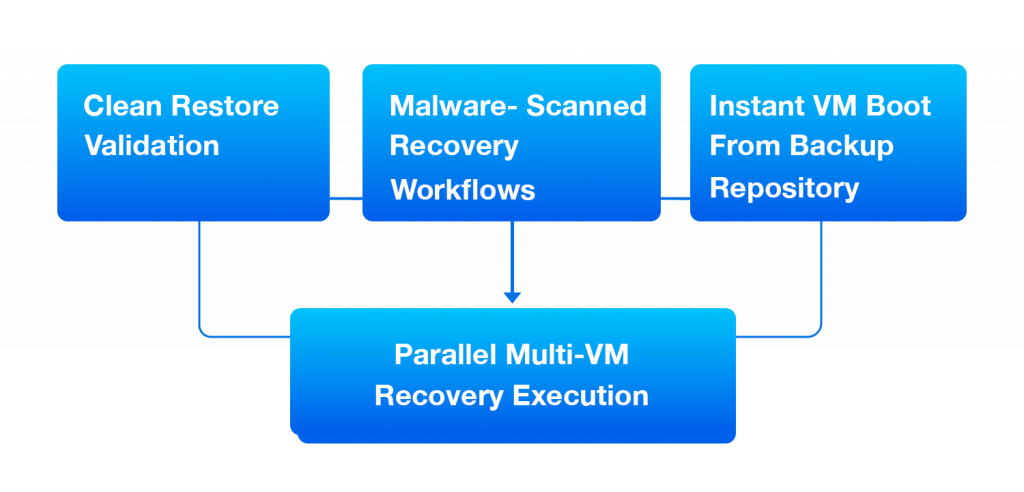
Clean, validated recovery with instant multi-VM restoration capability
Clean restore validation
Malware-scanned recovery workflows
Instant VM boot from backup repository
Parallel multi-VM recovery execution
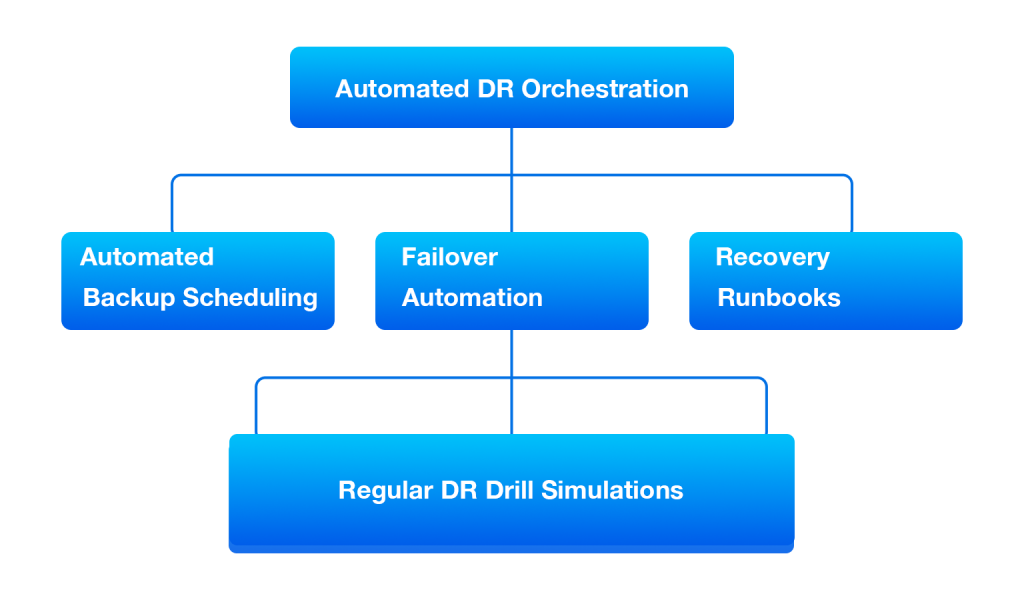
Automated DR Orchestration
Policy-driven failover automation with predefined recovery execution workflows
Policy-based backup scheduling
Scripted failover workflows
Predefined recovery runbooks
BI-Annual DR drill simulations